By Michael Riley
Target was striving to be different. Company officials say its information security staff now numbers more than 300 people—a tenfold increase since 2006, says one of the chain’s former information security managers. Less than a year before the Thanksgiving attack, Target brought in FireEye, a security software company in Milpitas, Calif., that was initially funded by the CIA and is used by intelligence agencies around the world.
The system works by creating a parallel computer network on virtual machines. Before data from the Internet reach Target, they pass through FireEye’s technology, where the hackers’ tools, fooled into thinking they’re in real computers, go to work. The technology spots the attack before it happens, then warns the customer. Unlike antivirus systems, which flag malware from past breaches, FireEye’s isn’t as easily tricked when hackers use novel tools or customize their attack, customers say. “It’s a very smart approach,” says Robert Bigman, the CIA’s former chief information security officer. “When we first started working with them several years ago, no one ever thought of doing it that way.”
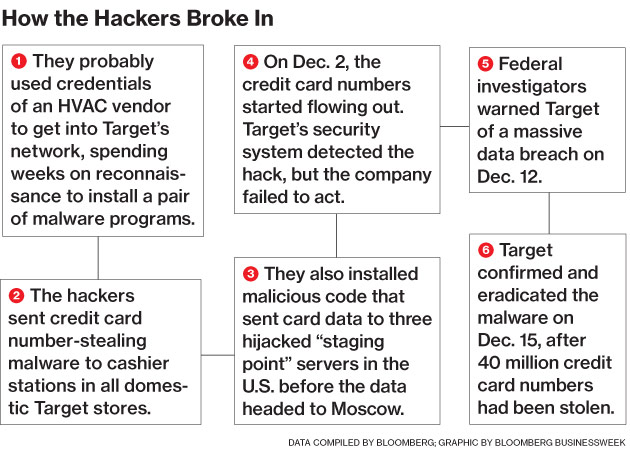
On Nov. 30, according to a person who has consulted on Target’s investigation but is not authorized to speak on the record, the hackers deployed their custom-made code, triggering a FireEye alert that indicated unfamiliar malware: “malware.binary.” Details soon followed, including addresses for the servers where the hackers wanted their stolen data to be sent. As the hackers inserted more versions of the same malware (they may have used as many as five, security researchers say), the security system sent out more alerts, each the most urgent on FireEye’s graded scale, says the person who has consulted on Target’s probe.
The breach could have been stopped there without human intervention. The system has an option to automatically delete malware as it’s detected. But according to two people who audited FireEye’s performance after the breach, Target’s security team turned that function off. Edward Kiledjian, chief information security officer for Bombardier Aerospace, an aircraft maker that has used FireEye for more than a year, says that’s not unusual. “Typically, as a security team, you want to have that last decision point of ‘what do I do,’ ” he says. But, he warns, that puts pressure on a team to quickly find and neutralize the infected computers.