I’ve recently been using the final, Released to Manufacturing version of Windows 8 on one of my computers, to much delight. I’ve been very impressed by how fast, well-designed, functional and capable this latest iteration of Windows is. However, my tinkering around from a security/privacy perspective has left me concerned.
Nadim Kobeissi may be young, but already the hacker and programmer has done more to fight for privacy and internet rights than most of us ever will. Now, he sheds light on the fact that Microsoft knows everything we install on our Windows 8 devices.
Windows 8 has a new featured called Windows SmartScreen, which is turned on by default. Windows SmartScreen’s purpose is to “screen” every single application you try to install from the Internet in order to inform you whether it’s safe to proceed with installing it or not. Here’s how SmartScreen works:
1. You download any application from the Internet. Say, the Tor Browser Bundle.
2. You open the installer. Windows SmartScreen gathers some identifying information about your application, and sends the data to Microsoft.
3. If Microsoft replies saying that the application is not signed with a proper certificate, the user gets an error that looks something like this.
There are a few serious problems here. The big problem is that Windows 8 is configured to immediately tell Microsoft about every app you download and install. This is a very serious privacy problem, specifically because Microsoft is the central point of authority and data collection/retention here and therefore becomes vulnerable to being served judicial subpoenas or National Security Letters intended to monitor targeted users. This situation is exacerbated when Windows 8 is deployed in countries experiencing political turmoil or repressive political situations.
This problem can however get even more serious: It may be possible to intercept SmartScreen’s communications to Microsoft and thus learn about every single application downloaded and installed by a target. Here is my analysis:
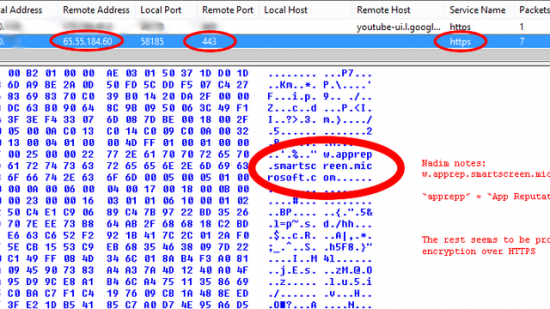
A quick packet capture showed the following activity happening immediately when I tried to install the Tor Browser Bundle:
SmartScreen appeared to connect over HTTPS to a server in Redmond (apprep.smartscreen.microsoft.com, 65.55.184.60, run by Microsoft) in order to communicate information about the application I was trying to install.
After running some tests on this Microsoft server, I discovered that it ran Microsoft IIS 7.5 to handle its HTTPS connections. The Microsoft server is configured to support SSLv2 which is known to be insecure and susceptible to interception. The SSL Certificate Authority chain goes down from “GTE CyberTrust Global Root” to “Microsoft Secure Server Authority.” The Certificate Authority model is itself susceptible to some serious problems.