Crikey.com.au
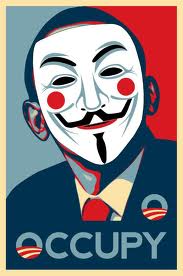
An Australian activist is fighting an attempt by Boston authorities to subpoena information about her from Twitter in relation to the #occupy movement.
Asher Wolf, a transparency and information activist, is based in Melbourne and over the past 18 months has quietly become one of the key people on Twitter for following news about transparency issues, WikiLeaks, net surveillance and the Occupy movement, via her extensive and systematic retweeting of information from around the world.
Just before Christmas, she learnt that the Boston District Attorney Benjamin A. Goldberger had contacted Twitter and demanded user information about “Guido Fawkes, @p0isonANon, @occupyBoston, #BostonPD, #d0xcak3” in what is called an administrative subpoena, commonly issued by law enforcement agencies to holders of information such as telecommunications companies.
The subpoena itself is bizarre and quickly became an internet laughing stock, as it got the #occupy account for Boston wrong (it’s @occupy_Boston, inter alia), it spelt @DoxCak3 wrongly, and purported to subpoena information about any account that used the hashtags #BostonPD and #d0xcak3. (“Guido Fawkes” isn’t a reference to the British blogger but the pseudonym of the holder of the account @p0isonANon i.e. it’s redundant).
But in trying to subpoena a hashtag, the Boston DA, one Benjamin A. Goldberger, either through a lack of understanding of social media, or as part of an extraordinary international fishing expedition, has sought information about anyone who used the hashtags in a tweet during the dates identified in the subpoena.
Goldberger also demanded that Twitter keep the subpoena secret, a request rejected by the company in the absence of any legal basis for it. Twitter last year defeated an attempt by the Department of Justice to keep secret a judicial order demanding information on users associated with WikiLeaks.
Australian lawyers Doogue & O’Brien, acting for Wolf and another, have told Goldberger and Twitter that they will resist the subpoena, given its broad scope and the “fishing expedition” nature of the request. “The ultimate effect of your subpoena is to pose a direct challenge to our client’s right to free speech. This is particularly concerning in light of the fact that one of our clients is a journalist who uses Twitter, amongst other media, to report on current affairs. Twitter encourages the free flow of information and reportage. The course which you have taken will inevitably stifle this important function.”
How much standing Twitter’s Australian users have is unclear. The user @p0isonANon, with assistance from the American Civil Liberties Union, is currently seeking to overturn the subpoena in the Massachusetts courts. But the subpoena is directed to Twitter, and it is up to the company, which is registered in Delaware and headquartered in San Francisco, to determine its compliance. Lawyer Bill Doogue says the current goal is to get more information, particularly about the criminal investigation the subpoena says is currently under way. “The simple step of subpoenaing a hashtag captures people doing nothing wrong or potentially wrong — so why should their details be made available?” Doogue says, “But the essence is that Twitter shouldn’t be logging details like IP addresses.”
WikiLeaks recently launched a campaign to encourage Twitter, considered the most liberal-minded major social media company for its efforts to fight the Department of Justice, to end logging of real-time user information such as IP addresses. “In a progressive company concerned with protecting privacy and security of user data — the defacto position should be no data retention,” says Wolf.
The broader issue here is how governments (and the corporations they frequently act at the behest of) are seeking to respond to the borderless nature not so much of the internet itself as of internet communities. The issue takes a number of forms: the UK legal industry maintains it has a form of extraterritorial jurisdiction, and has so aggressively asserted its right to silence people via internet-related libel cases that US lawmakers have responded. But at the same time, the United States assumes an almost unlimited extraterritoriality in the application of its laws, both generally and specifically on online issues — the NDAA signed by Obama recently arrogates to the US military the power to abduct and indefinitely detain anyone considered to be linked to the War on Terror; British student Richard O’Dwyer is to be extradited under anti-terror legislation to face a decade in jail in the US merely for building a website that linked to filesharing sites.
However, when the world’s biggest social media companies are based in the US, governments there need no extraterritoriality, leaving users in any country using sites like Facebook and Twitter, or services like Google, liable to monitoring by the US government or state agencies via US law.
As Wolf points out, geographic segmentation is currently a standard feature of internet commerce, which means that in effect non-US internet users get the worst of both worlds when it comes to the borderless internet: they are subject to US monitoring of social media networks but often can’t access the full benefits of US internet commerce. “If Amazon and iTunes can segment their markets for restrictive purposes,” Wolf says, “then why not Twitter, to meet legal requirements enacted by countries demanding privacy protection for their citizens?
“If the Australian government wanted to protect its citizens it could legislate to protect data owned or generated by Australian citizens — by enacting strict laws against data retention,” she says. “For instance, the government could legislate companies wishing to do business with Australian citizens must delete data and traffic logs after a period of no more than three months after Australian citizens deleting their personal material. Australia should also place pressure on fellow common law countries to bring in similar legislation.”
The only real solution is social media networks outside the jurisdiction of nation-states. WikiLeaks is currently establishing its own social network, Friends of WikiLeaks, and Anonymous has established AnonPlus; there have also been anonymous microblogging sites such as Youmitter established, but their lack of critical mass is a key impediment, as is resilience in the face of surges in traffic, and they remain vulnerable, to the extent that it’s enforceable, to authorities claiming to exercise jurisdiction over whatever servers are used to host the networks.

