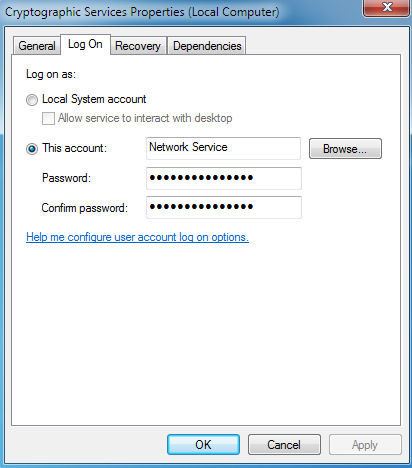
Provides four management services: Catalog Database Service, which confirms the signatures of Windows files and allows new programs to be installed; Protected Root Service, which adds and removes Trusted Root Certification Authority certificates from this computer; Automatic Root Certificate Update Service, which retrieves root certificates from Windows Update and enable scenarios such as SSL; and Key Service, which helps enroll this computer for certificates. If this service is stopped, these management services will not function properly. If this service is disabled, any services that explicitly depend on it will fail to start.
Path to executable: C:\windows\system32\svchost.exe -k NetworkService
-Command used: netstat -bo 10 > C:\netstat.txt
Then you get this below:
TCP 192.168.1.100:49175 64.4.11.42:http ESTABLISHED 1324 CryptSvc [svchost.exe]
As you can see this connection runs automatically as a service and has a login/password to this service. This account doesn’t exist under management users/groups. If you type 64.4.11.42 in your web browser it will resolve to Microsoft. The most concerning of all this….a Crypto service is connecting to a HTTP non secured unencrypted web server….