An online service that claims to offer 46 million users a free and secure way to browse the web anonymously is plagued with issues that allow customers to be tracked and hacked, security researchers say.
Hola is an Israeli-based browser plugin that since 2008 has given users the ability to surf the web by routing traffic through the connections of others–a feature the company has touted as a means of bypassing restrictions, such as country-specific censorship.
However, on Friday this week, a small group of security experts announced that multiple vulnerabilities within the application can seriously compromise the security of its customers. Hackers can actually remotely execute any type of code with system-level privileges on machines of potentially millions of Hola users.
According to the team that discovered the flaws–an internationally dispersed group of researchers and developers, including former members of the infamous hacking group LulzSec–issues with both Hola’s code and the company’s corporate policies pose a number of problems.
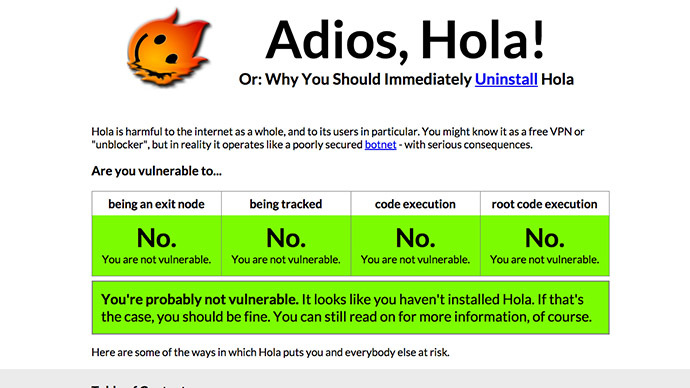
You might know it as a free VPN or ‘unblocker’,” the researchers said, “but in reality it operates like a poorly secured botnet – with serious consequences.”
On Hola’s website, the company explains that by sending browser traffic through other nodes in its network, a user in Moscow may be able to surf the web as if they were in Manhattan, “making your IP harder to track,” according to the site, and “thus allowing you to be more anonymous and secure.”
“Hola lets you have access to information that is otherwise not available in your geography while protecting your online privacy,” the company explains on its website. “We have built Hola for you, and with your privacy and security in mind,” it boasts.
Yet in the “Adios, Hola!” report published on Friday, the researchers say users of the supposedly privacy-minded plug-in can actually be tracked while they browse the web because of a bug that lets remote sites see potentially personal information about the Hola user’s computer, including uniquely crafted IDs that differ with each installation.
More critical, however, is their assertion that any of the millions of users could end up having their entire computer compromised due to an error in the software’s code: if a user is navigating web pages with the Hola plugin, a simple click of a link on a malicious site is all it would take for a hacker to remotely execute any type of code on the victim’s machine, the researchers say.
“They let anybody execute programs on your computer,” the report claims. To prove as much the researchers have embedded a link in their report which, when clicked, launches the targeted computer’s calculator application.
“We’re nice people, so we just made a button that opens a calculator for you,” the researchers wrote. “Somebody with more… malicious goals could have easily done the same, but invisibly, automatically and with a piece of malware instead of a calculator. They could take over your entire computer, without you even knowing.”
“It’s worrying when you see poorly designed security products; it’s even worse when you see privacy products that appear to be created specifically to take advantage of people looking for safety online,” Morgan Marquis-Boire, a senior researcher at University of Toronto’s Citizen Lab, told RT’s Andrew Blake on Friday.
The flaw has been in the plug-in since at least 2013, the group says, and the remote code execution vulnerability can be exploited in the FireFox add-on on computers operating Windows. Other browsers and operating systems, including mobile devices, are vulnerable to the exploit that discloses personal user details, the researchers say.
With regards to being able to remotely execute code on a targeted machine, the researchers say Hola users face potentially dire consequences.
“If an attacker can perform a Man-in-the-Middle attack against a target running the Hola client on Windows – either as a network adversary, ISP, intelligence agency or another Hola client acting as an exit node — they can create a connection seeming to originate from the hola.org or client.hola.org hosts to the local websocket port,” the report reads. From there, code can be executed by a hacker thousands of miles away, the result of which could give attackers control over entire systems.
Ofer Vilenski, the cofounder of Hola, told Motherboard on Friday that “there’s absolutely no way that we know of to do that, nor have we ever heard such a claim.”
“This kind of security issue can only happen if a developer is either grossly incompetent, or simply doesn’t care about the security of their users. It’s negligence, plain and simple, and there’s no excuse for it,” the researchers said.
According to the group, the only way to avoid being potentially exploited by the bug is to uninstall Hola.